Privacy and the IPhone, Who do you trust more, Uncle Tim or Uncle Sam | Eastern NC Now
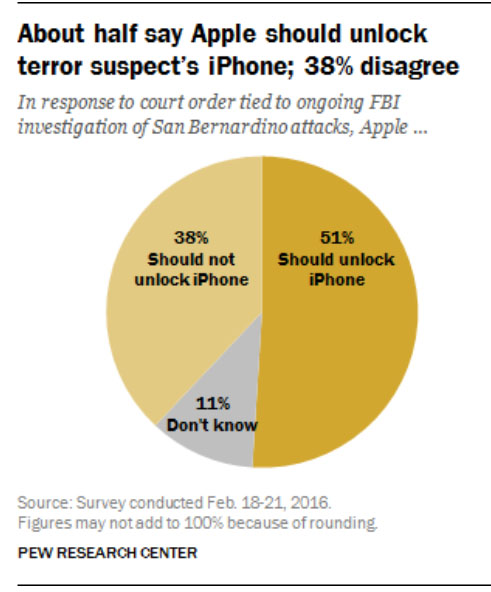
There has been a firestorm about the FBI request for Apple to break the IPhone of the San Bernardino terrorist's.

 request for Apple to create a backdoor, or entry to the IPhone of the terrorist from San Bernardino, I would suggest that you review the video below. It is a passionate defense of privacy by Ted Olson, who lost his wife in the 9/11 Terrorist attacks and is a former Solicitor General of the US.
request for Apple to create a backdoor, or entry to the IPhone of the terrorist from San Bernardino, I would suggest that you review the video below. It is a passionate defense of privacy by Ted Olson, who lost his wife in the 9/11 Terrorist attacks and is a former Solicitor General of the US.
 When you make a phone call or add a contact to you IPhone, do you have some expectation that it will remain private? The phone call is captured by the carrier of your choice. A court order can force them to provide the government with listing of your calls to and from but not the content.
When you make a phone call or add a contact to you IPhone, do you have some expectation that it will remain private? The phone call is captured by the carrier of your choice. A court order can force them to provide the government with listing of your calls to and from but not the content.
|
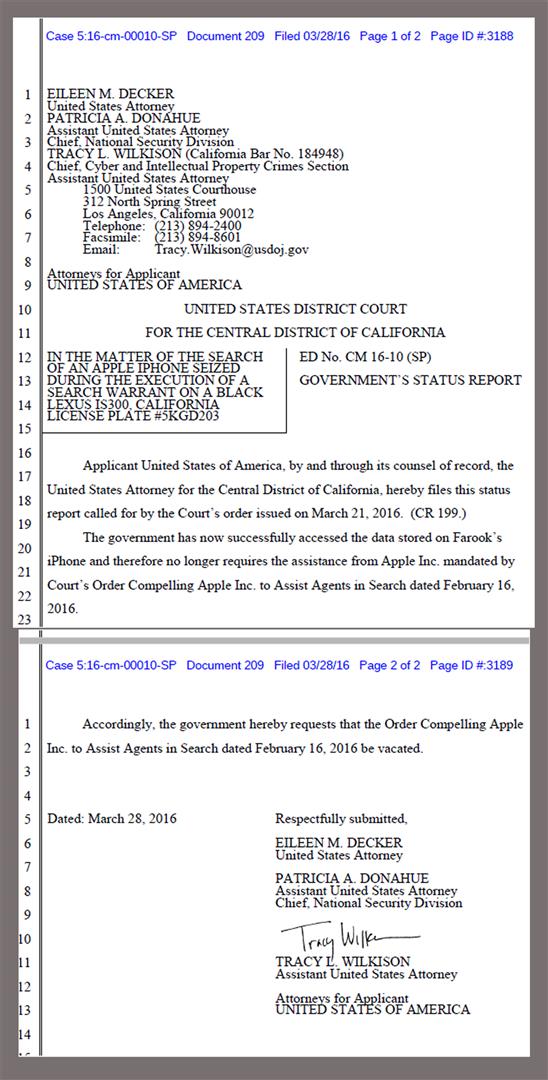
Update
FBI Says It May Be Able To Access Shooter's iPhone Without Apple's Help www.npr.org BT Disclaimer: I keep adding these updates because it is your and my privacy at stake. I believe that the FBI is not actually asking for access to the information but is trying to set a legal precedent for forcing a company to create something that the government should be able to do on its own with proper search warrant protections. |
|
More attacks coming after biggest hacker breach in Apple app store
"Apple's (AAPL) iPhone app store was penetrated by hackers who infected hundreds of apps with malware -- including the Chinese version of Angry Birds 2 and WeChat -- but the malevolent programmers didn't actually crack Apple's security, they bypassed it". finance.yahoo.com |
|
There is apparently a legal way to obtain the information from this IPhone but I have my concerns on the basic premise of the government forcing the manufacturer to provide a mechanism to defeat one of its features. That makes the manufacturer responsible for the use of something that is nothing more than a tool. Many will interpreted my opinion as opposed to breaking into the phone. That would be incorrect; I am more concerned about the principal. If there is data on that phone that is relevant to future actions, I am sure it will have been altered or changed by the potential terrorist because it is compromised.
What would be next, knifes, scissors, or rocks. There is a parallel to the torture of prisoners to gain information. No matter how important the information is the end may not justify the means without full due process under the law. It is not a small step after that to require the gun and ammunition manufactures to be responsible for the use of their product. I am in 100% percent support of cracking the IPhone but it should not be the responsibility of the manufacturer to provide the mechanism. I am sure there is enough hackers around who could jailbreak this phone and like I mentioned below, the Chinese may already have methods at hand defeat any encryption. I pay close attention to the legal arguments regarding this as opposed to the emotional appeals about the possible outcome. We are on slippery ground when we bend any constitutional prohibitions in the name of safety. Maybe we can get Diane Rufino to weigh in on this matter. |
|
I am not a phone guy. As a tool that I have to have, I have become a pretty good computer guy. I use it to create stuff.
As one who is code empathetic, I believe that we have much to learn, and I believe that there is a way to serve both needs - code safety and national security. |
|
Here is some more ideas for thought. The Iphone is made and assembled in China. The CPU used in the IPhone is designed by Apple but built and assembled in China. It would be easy to hardwire a backdoor in the CPU that can bypass the security of the operating system. I am way out of my element here but I have found that for every software problem there is a solution. One of the few things I trust less than my own government is the Chinese government. It is possible that they have already hardwired a backdoor into the chips that they can access at will by a special security code only they know.
There are two arguments here in my mind. 1) Does the American Government have the right to require a private company to create a bypass for a product they created when one of it's major selling features is an encryption of the data and security from hackers? One of Steve Job's pet believes was that the IOS is closed sourced. Only approved applications can be loaded on an Iphone where as Android and Windows are open sources with the operating system subject to manipulation. 2) Has there ever been any system that is not breakable? Just because I am paranoid, blah, blah, blah. See the link below on the Manufacturer of the Iphone chipset. en.wikipedia.org |
|
Great post Bobby Tony - Really lays it all out.
It is a real 'header scratcher' of an issue - civil liberties vs civil protection. It just seems that if there are terrorists, there could be security protocols put into place, where code could be written in a secure place that would stay there, thus discovery could be made from that safe place. You know, I forgot about the Democrats, like Hillary Clinton, and her followers, who believe that a Democrat can be president without being a patriot. How safe would that code be with Hillary or fellow non patriot Hussein at the wheel? And then the conundrum becomes more complex. |
| Do Roy Cooper, Deborah Ross and Other Democrats Want to Bring Terrorists to North Carolina? | Views from the Right Seat, Editorials, Op-Ed & Politics | You Gain From New Businesses |
In 2014 the NSA agency's Michael Daniel Special Assistant to the President and Cybersecurity Coordinator released the following information. It is barely possible that the FBI may have to disclose to Apple how it hacked the IPhone. I would not hold my breath but Apple could contract the same company the FBI used to find out how they broke the system.
"This spring, we re-invigorated our efforts to implement existing policy with respect to disclosing vulnerabilities – so that everyone can have confidence in the integrity of the process we use to make these decisions. We rely on the Internet and connected systems for much of our daily lives. Our economy would not function without them. Our ability to project power abroad would be crippled if we could not depend on them. For these reasons, disclosing vulnerabilities usually makes sense. We need these systems to be secure as much as, if not more so, than everyone else."
www.whitehouse.gov